What is information security, and why does it matter?
Information security is the practice of protecting information, typically to preserve its confidentiality, integrity, and availability. These three properties, also known as the CIA triad, serve as a foundational set guiding our thinking about security of information.
- Confidentiality means information is only accessed by those it is meant for
- Integrity means information stays accurate and complete, and is only changed deliberately, by the right people
- Availability means information is there when you need it
Every organisation has its own reasons for protecting information, shaped by what the business does, who it serves, and what it is trying to achieve. A payment processor’s security objectives look different from a hospital’s, which look different from a defence contractor’s, for example. What matters is that security objectives must align with what the organisation is trying to accomplish.
This sounds like a cliché, and it’s easy to overlook. But there is a reason every information security framework repeats it.
Information security is a business function
It’s common for people to use the terms “information security” and “cybersecurity” interchangeably, and this is not completely wrong. The practical difference is nuanced for the everyday person. But where the two terms differ significantly is in how they relate to the business.
When people talk about cybersecurity, they typically consider it a technical function. Cybersecurity focuses on securing digital infrastructure (like networks, endpoints, etc.) and data. Traditionally it has been positioned as a sub-function of the IT department.
Information security is broader, taking care of the security of information in all its forms — not only digital data and infrastructure, but also paper copies, verbal and other types of analogue communication, memorised information, etc. Instead of focusing solely on technology, information security also looks at people and processes. As such, it is typically positioned as a core business function that reaches across departments.
That is why security objectives must align with and support the organisation’s strategic goals. Otherwise, security becomes a burden, another cost centre that management tries to avoid.
Why it matters now more than ever
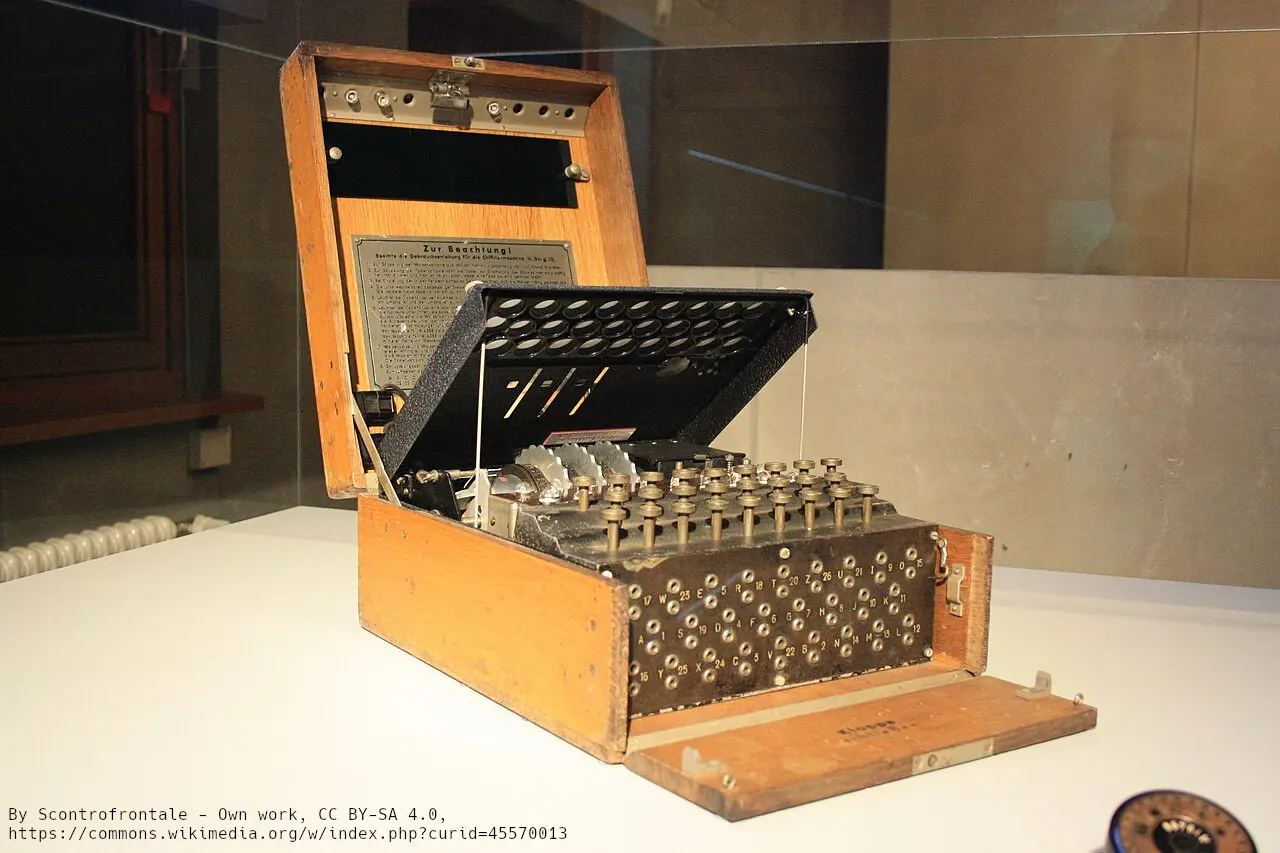
If you are ever near Berlin, you should visit the Berlin Spy Museum. Besides having very intriguing exhibits, it is a good reminder of the extent to which people are willing to go for gathering and protecting information.
Information has always been a valuable asset. People, businesses and states have always sought information to gain a societal, economic, political or military advantage. Since the rise of computer technology, the scale at which we exchange information has increased dramatically, accelerating further with every technological breakthrough: personal computers, the internet, smartphones, and now generative AI.
In the past few decades, a large portion of our economy has moved into the digital space, becoming ever more reliant on the rapid exchange of information. And, unfortunately, so has warfare.
Things are getting personal
The more our economy depends on information, the more there is at stake when it is compromised. Disruptions to supply chains, ransomware shutting down hospitals and pipelines, state-sponsored attacks on critical infrastructure — these are no longer hypothetical scenarios. They are regular occurrences, and they have caught the attention of regulators.
The response across Europe has been a wave of legislation demanding better resilience from organisations that the economy depends on. The EU’s NIS2 Directive dramatically expands the scope of who is covered. DORA targets the financial sector and its ICT suppliers. The Cyber Resilience Act sets security requirements for products.
What makes these regulations different from earlier efforts is that they do not stop at the organisation. They hold management personally accountable for ensuring that security is governed properly. Directors and executives who fail to meet their obligations face direct consequences.
Information security is no longer something leadership can delegate and forget about.
A structured approach to security: ISMS
Faced with these challenges, how do we manage information security in a way that is systematic, proportionate, and sustainable?
The answer is an Information Security Management System, commonly referred to as an ISMS. It is a structured approach to managing information security through policies, processes, roles, and controls, all driven by risk-based decisions .
It is not a product you buy, a checklist you complete, or a one-time project that ends with a certificate on the wall. It is an operating system for making security decisions and demonstrating that those decisions are sound.
The international standard for ISMS is ISO/IEC 27001. It provides a framework for establishing, implementing, maintaining, and continually improving information security management. The standard is deliberately technology-neutral and sector-agnostic. It does not prescribe specific controls or tools. Instead, it requires the organisation to assess its own risks, determine what controls are appropriate, implement them, monitor their effectiveness, and improve over time.
There is a catch, though. Having an ISMS does not mean you are secure. It means you have a system in place that enables you to identify and address issues. But you need to be diligent, responsible, and actually do it. Otherwise it’s only a compliance theatre, with no real security benefits.
ISO/IEC 27001 includes Annex A, a catalogue of 93 controls across organisational, people, physical, and technological domains. Its purpose is not to serve as a compliance checklist, but rather offer a broad and relatively complete set of controls that organisations can use to identify weaknesses and mitigate risks. Some controls will be essential; others will be irrelevant to your context; and for some risks you might still need to look elsewhere for a solution.
What comes next
In this series we will go through some of the steps of building and running an ISO/IEC 27001 compliant ISMS. The first of them is understanding the environment — the organisational context — in which the ISMS will exist. In the next post in the series we will look at some techniques on how this can be done.
